GoldenEye, the ransomware that attacks sending resumes
During the first months of 2016, we witnessed the irruption of Petya : a ransomware that was installed in the boot sector of the hard disks that it infected and then encrypted them completely. This malware was to increase the lists of the cryptographic ransomwares, of which Cryptolocker is one of its most typical examples.
 Thanks to ZDNet we have known the existence of GoldenEye, a successor of Petya that works in the same way, with a very curious purpose and form of attack: human resources departments of companies. It tries to enter the computers of those who are in charge of the selection of personnel through emails with attachments that try to impersonate legitimate requests for employment.
Thanks to ZDNet we have known the existence of GoldenEye, a successor of Petya that works in the same way, with a very curious purpose and form of attack: human resources departments of companies. It tries to enter the computers of those who are in charge of the selection of personnel through emails with attachments that try to impersonate legitimate requests for employment.
Security researchers at Check Point have been monitoring their expansion campaign, which has attempted to deliver malware to targets based in Germany using the attack method just described.
This is how an infection works with GoldenEye
When GoldenEye tries to enter a computer it does so using two files. The first is a PDF that does not contain malicious software, but is aimed at trying to make the target think that it is a standard job request. The second is an Excel file that supposedly contains a form with a job application.
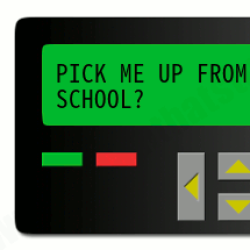
This excel file is where malware is hidden. When the target opens it is presented with a document that says to be “loading”, and requests that the macros be enabled to open. When this is done, a code is executed that begins to encrypt the files of the computer before presenting the note that heads these lines.
To get rid of the scourge of GoldenEye you have to pay 1.3 bitcoins, which to the change are more than 950 euros. The rescue note details the victim how he can buy bitcoins on the dark web and even offers to exchange messages with a malware administrator if they have problems with payment or the decryption process.
One way to prevent users from becoming infected with this ransomware is to not enable macros in Microsoft Office documents, and to use common sense when receiving unexpected or overly generic emails. Another option is to use an anti-virus like RansomFree.